If you missed this one; please head to this link, and try it yourself before going to the solution.
.
.
.
.
.
.
I quickly recognized this must be a pcap dump, or a snap from a binary file (i.e. raw disk dump)
so I opened up a hex editor; I was on Windows so I used: HxD
this is what it looked like:

you quickly notice the corrupted bytes, so I corrected 3 bytes and noticed the changed values;
For example: “evånt” should have been “event”
hence “65 76 E5 6E 74″ should have been “65 76 65 6E 74″
I ended up with this algorithm:
search for any byte that is more than 0x8
substitute 0x8 from it
0xf -> 0x7
0xe -> 0x6
0xd -> 0x5
etc..
after it’s done you get a clear uncorrupted ascii, which looks like a part of an event log.
At this point you also get old and new passwords.
- “old_password”: “:\xC7\xF4\n\xAF))7C\x15\xD0\xF3\xDEiU;”,
- “new_password”: “9\xFA\x99\xCA\xED\xF2XSG\xDD-\xC2\x8EzHk”,
Very quickly you notice these are in hex format (thanks OSCE!); I looked at the hex equivilent and converted them manually; however a smarter way would have been python’s hexlify (yep there is a thing for that).
|
1 2 3 4 5 |
import binascii pwd = ":\xC7\xF4\n\xAF))7C\x15\xD0\xF3\xDEiU;" binascii.hexlify(pwd) # output : '3ac7f40aaf2929374315d0f3de69553b' |
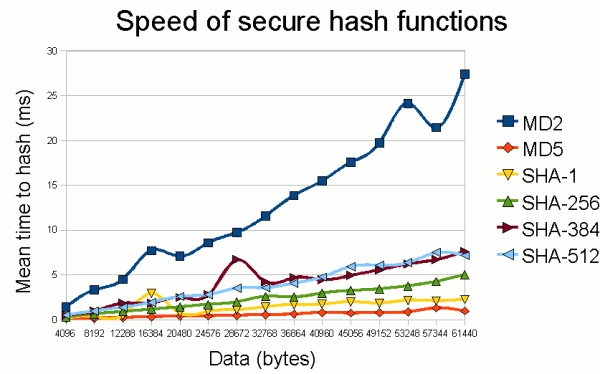
I quickly headed up to the wiki page of hashes and figured this must be an md5.
at this point I spent hours trying to brute force them, until I thought maybe I need to try salt? double md5?
Everything failed until I tried md5(reverse(hash))
again python comes handy 🙂
|
1 2 3 4 |
binascii.hexlify(pwd)[::-1] # 'b35596ed3f0d5134739292faa04f7ca3' binascii.hexlify(npwd)[::-1] # 'b684a7e82cd2dd7435852fdeac99af93' |
then feed them to the monster crackstation.net
final results:



Leave a reply