Intro
I was lately surprised by my new ‘Ubuntu Server’ computer connecting back to a strange IP address: 91.189.92.11 on port 443! I immediately started investigating the case and did a whois lookup on the IP address to discover that the IP points to this domain productsearch.ubuntu.com – a page that will display a 403 Forbidden Error.
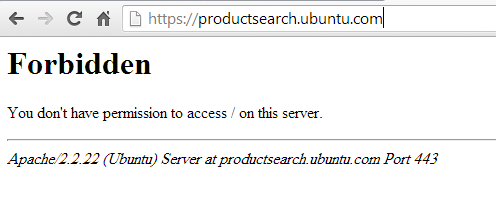
What is productsearch.ubuntu.com?
So apparently according to this website: If you’re an Ubuntu user and you’re using the default settings, each time you start typing in Dash (to open an application or search for a file on your computer), your search terms get sent to a variety of third parties, some of which advertise to you. Ubuntu should protect user privacy by default. Since it doesn’t, you can use the code to the left to disable the parts of Ubuntu which are invasive to your privacy.
You can also read more about Ubuntu 3rd parties: http://www.ubuntu.com/privacy-policy/third-parties
So what to do about this?
First I would like to mention this Softpedia GUI-like solution to this issue.
Alternatively you can DIY – You need to run this script, which is self explanatory:
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 |
#!/bin/bash GS="/usr/bin/gsettings" CCUL="com.canonical.Unity.lenses" # Figure out the version of Ubuntu that you're running V=`/usr/bin/lsb_release -rs` # The privacy problems started with 12.10, so earlier versions should do nothing if awk "BEGIN {exit !($V < 12.10)}"; then echo "Good news! This version of Ubuntu is not known to invade your privacy." else # Turn off "Remote Search", so search terms in Dash don't get sent to the internet $GS set $CCUL remote-content-search none # If you're using earlier than 13.10, uninstall unity-lens-shopping if [ $V \< 13.10 ]; then sudo apt-get remove -y unity-lens-shopping # If you're using a later version, disable remote scopes else $GS set $CCUL disabled-scopes \ "['more_suggestions-amazon.scope', 'more_suggestions-u1ms.scope', 'more_suggestions-populartracks.scope', 'music-musicstore.scope', 'more_suggestions-ebay.scope', 'more_suggestions-ubuntushop.scope', 'more_suggestions-skimlinks.scope']" fi; # Block connections to Ubuntu's ad server, just in case if ! grep -q "127.0.0.1 productsearch.ubuntu.com" /etc/hosts; then echo -e "\n127.0.0.1 productsearch.ubuntu.com" | sudo tee -a /etc/hosts >/dev/null fi echo "All done. Enjoy your privacy." fi |
I also added couple of iptables rules to block any access to that host and IP
iptables -I FORWARD -d 91.189.92.11 -j DROP
iptables -I OUTPUT -d 91.189.92.11 -j DROP
iptables -A OUTPUT -m string --string 'productsearch.ubuntu.com' --dport 443 -j DROP
iptables-save
You’re not done yet. A session to productsearch.ubuntu.com must have been taken place earlier and you need to ‘kill’ it.
You can do that using tcpkill, but I prefer this method:
first get all actively listening processes: ss -aunt, note the PID of the process, then kill it using process name: pkill unity-scope-hom or PID kill #PID#
now recheck if there is any active connections to that host ss -aunt
Your system should be clean now.


Leave a reply