If you missed this one; please head to this link, and try it yourself before going to the solution.
Read More

I’m a great believer in automation; as one of my interviewers said to me once: If we do it twice; we automate it.
I adopted this style throughout my work; hence I wanted to show how would I upgrade/update the WordPress core and plugins using cron to keep all my blogs and sites secure and up to date with security patches.
1- get & install wp-cli (how/where)
2- write a script to use wp-cli to update WordPress [see attached code]
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 |
#!/bin/bash # prevent errors snowball effect : stop at any process which exit with non success value (non zero) set -e # print current version | used for logs wp core version # upgrade core and database wp core update wp core update-db # upgrade plugins wp plugin update |

Wait; did I say BackTrack? Yes Backtrack is still a cool (outdated) distro for hacking!
If for some odd reasons you still need to use BackTrack in 2017 (hello? have you heard of Kali), I won’t judge you.
Maybe you’re doing your OSCE and need an image that is still in the course / labs
This post is meant to save you some time if you haven’t used BackTrack for a while and need to get some things done with it.
1. We want to change the root password
|
1 |
passwd |

Recently I was working on one of the vulnhub vulnerable boxes and once I finally got a reverse shell it was a restricted one. What a bummer!
In this post I want to document how did I breakout of it in a simple way.
There many ways to break out of the restricted shell (aka /bin/rbash). One simple way for example is to use perl or python to call /bin/sh:

Perl/Python aren’t the only ways. You can STILL breakout if vim, vi, awk, gdb, more, less, etc. are allowed!
What I want to add here is a special case of a restricted bash, that’s when the rbash is called with an output redirection.
So might be able to use the earlier tricks to breakout but it’s no good as all the output is being r...
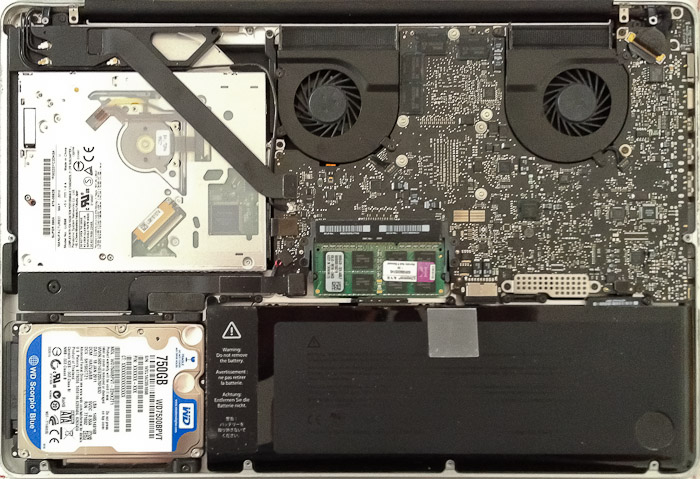
back in the summer of 2016 I was eating an orange while working just to end up with a drop of orange liquid inside the keyboard of my beloved macbook.
I am very attached to this macbook since years, and this juice decided to ruin the worst possible key [SHIFT] in the mac, hence all I was able to write is capital letters, the booting won’t work because it MAC OS boots to safe-mode by default if the shift key is pressed on booting time. Even worse than this all was not able to login into my environments because the all my passwords were capitalized.
Back then I decided to override the [SHIFT] key using a software interupt, which worked greatly until I decided to replace the whole macbook keyboard. The process of replacing the keyboard wasn’t that complicated, what came next was 🙂
Upon bo...
Read MoreNote: This post is part of the “20p Everyday” project.
I was fortunate enough to attend one of the best information security schools in the world. Yes that’s Royal Holloway University of London after a long academic journey, ups and downs of course..
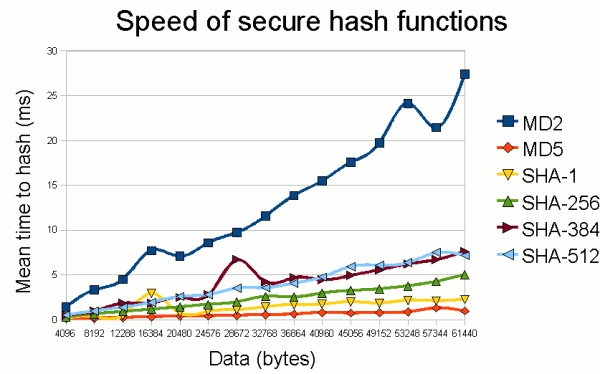
I was even more fortunate to have the author of this book, Keith Martin, as one of my professor back in RHUL.
He taught me “Crypto 1”. I enjoyed his lecture very much. It was one of the most interesting lecture at times.
Personally I had some ideas about cryptology (the correct term btw.) since my computer security course I took with Fadi Aloul at the American University of Sharjah (AUS). I had an idea about
what is a public key what is a private key, and what’s PGP (pretty good privacy), thanks to Taha Landolsi and his course “Networks II” at...
We mentioned before how did we switch to SSL since 2017.
I want to add here how to set HSTS to prevent a wellknown SSL attack called SSL-Strip.
You can watch the full talk to understand in details how this works here.
Basically the attacker is somehow (we don’t care how) a MITM setting in between the victim and the authentic server.
The attacker in this case can do a downgrade attack on SSL and transfer all HTTPs connection to the normal plain text HTTP connections.
Now the attack can simply sniff all data being communicated between the victim and the server.
The attacker is also free now to change the data and execute other attacks such as injecting malware into the traffic.
HSTS or HTTP Strict Transport Security allows web servers to declare that web b...
Read MoreIn case you haven’t noticed. I’ve gone HTTPS with a green lock now 🙂

I also rate a “A” with Qualys’s SSL lab test. Check it here.

There is no more excuse not to be encrypting your traffic using TLS. A service like letsencrypt.org makes it so easy to switch to https you can finish the whole process in few mints (if not seconds!) using their certbot tool.
A quick guide to certbot can be found on youtube. If it doesn’t work by default, you will need to go the manual way. I might write a guide here when I have the time for it.
Keep encrypting!
Read MorePart of my 2017 goals is to read more, and not to make the common mistake not to be specific about my goals, I decided to precisely set to read 20 pages per day.
|–+ [ Everyday Cryptography [done][review]
|–+ [ The Hacker Playbook: Practical Guide To Penetration Testing [current]
|–+ [ The Hacker Playbook 2: Practical Guide To Penetration Testing [next]
As part of any post exploitation in a security auditing or testing engagement you will want to gather as much info as you want about the victim to be able to target your next victim in the chain.
Having said that sometimes you stumble upon strange files, encrypted data, and network traffic that you don’t know what to do with it. One of these was an .sdf file related to hmailserver. The last is an open source mail server, you can read more about it here.
When gaining access to this server you will want to read this file:
|
1 |
C:\Program Files\hMailServer\Bin\hMailServer.ini |
A sample output would look something like this:
|
1 2 3 4 5 6 7 8 9 |
Recent Comments