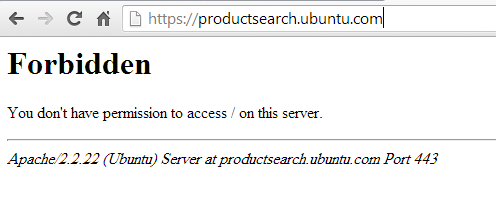
In case you haven’t noticed. I’ve gone HTTPS with a green lock now 🙂

I also rate a “A” with Qualys’s SSL lab test. Check it here.

There is no more excuse not to be encrypting your traffic using TLS. A service like letsencrypt.org makes it so easy to switch to https you can finish the whole process in few mints (if not seconds!) using their certbot tool.
A quick guide to certbot can be found on youtube. If it doesn’t work by default, you will need to go the manual way. I might write a guide here when I have the time for it.
Keep encrypting!
Read More


Recent Comments